
Practice Test #5
Simulasikan pengalaman ujian sesungguhnya dengan 50 soal dan batas waktu 45 menit. Berlatih dengan jawaban terverifikasi AI dan penjelasan detail.
Didukung AI
Jawaban & Penjelasan Terverifikasi oleh 3 AI
Setiap jawaban diverifikasi silang oleh 3 model AI terkemuka untuk memastikan akurasi maksimum. Dapatkan penjelasan detail per opsi dan analisis soal mendalam.
Soal Latihan
HOTSPOT - For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point. Hot Area:
The Service Level Agreement (SLA) guaranteed uptime for paid Azure services is at least 99.9 percent.
Companies can increase the Service Level Agreement (SLA) guaranteed uptime by adding Azure resources to multiple regions.
Companies can increase the Service Level Agreement (SLA) guaranteed uptime by purchasing multiple subscriptions.
You have an Azure environment that contains 10 virtual networks and 100 virtual machines. You need to limit the amount of inbound traffic to all the Azure virtual networks. What should you create?
HOTSPOT - For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point. Hot Area:
To achieve a hybrid cloud model, a company must always migrate from a private cloud model.
A company can extend the capacity of its internal network by using the public cloud.
In a public cloud model, only guest users at your company can access the resources in the cloud.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution. After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen. Your company has an Azure subscription that contains the following unused resources: ✑ 20 user accounts in Azure Active Directory (Azure AD) ✑ Five groups in Azure AD ✑ 10 public IP addresses ✑ 10 network interfaces You need to reduce the Azure costs for the company. Solution: You remove the unused user accounts. Does this meet the goal?
This question requires that you evaluate the underlined text to determine if it is correct.
If Microsoft plans to end support for an Azure service that does NOT have a successor service, Microsoft will provide notification at least 12 months before.
Instructions: Review the underlined text. If it makes the statement correct, select No change is needed. If the statement is incorrect, select the answer choice that makes the statement correct.
Ingin berlatih semua soal di mana saja?
Unduh Cloud Pass — termasuk tes latihan, pelacakan progres & lainnya.
This question requires that you evaluate the underlined text to determine if it is correct.
One of the benefits of Azure SQL Data Warehouse is that high availability is built into the platform.
Instructions: Review the underlined text. If it makes the statement correct, select No change is needed. If the statement is incorrect, select the answer choice that makes the statement correct.
HOTSPOT - You plan to implement several security services for an Azure environment. You need to identify which Azure services must be used to meet the following security requirements: ✑ Monitor threats by using sensors ✑ Enforce Azure Multi-Factor Authentication (MFA) based on a condition Which Azure service should you identify for each requirement? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point. Hot Area:
Monitor threats by using sensors:
Enforce Azure MFA based on a condition:
This question requires that you evaluate the underlined text to determine if it is correct.
From Azure Cloud Shell, you can track your company's regulatory standards and regulations, such as ISO 27001.
Instructions: Review the underlined text. If it makes the statement correct, select No change is needed. If the statement is incorrect, select the answer choice that makes the statement correct.
HOTSPOT - To complete the sentence, select the appropriate option in the answer area. Hot Area:
When you are implementing a Software as a Service (SaaS) solution, you are responsible for
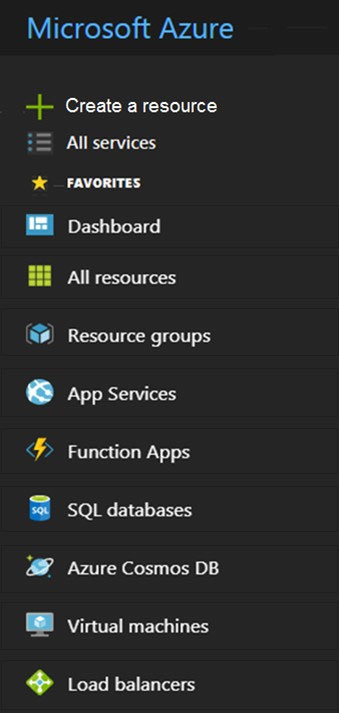
HOTSPOT - You need to request that Microsoft increase a subscription quota limit for your company. Which blade should you use from the Azure portal? To answer, select the appropriate blade in the answer area. Hot Area:
Select the correct answer(s) in the image below.
Tes Latihan Lainnya
Practice Test #1
Practice Test #2
Practice Test #3
Practice Test #4
Practice Test #6
Practice Test #7
Practice Test #8
Practice Test #9
Dapatkan aplikasi
