
Practice Test #2
Simulasikan pengalaman ujian sesungguhnya dengan 50 soal dan batas waktu 100 menit. Berlatih dengan jawaban terverifikasi AI dan penjelasan detail.
Didukung AI
Jawaban & Penjelasan Terverifikasi oleh 3 AI
Setiap jawaban diverifikasi silang oleh 3 model AI terkemuka untuk memastikan akurasi maksimum. Dapatkan penjelasan detail per opsi dan analisis soal mendalam.
Soal Latihan
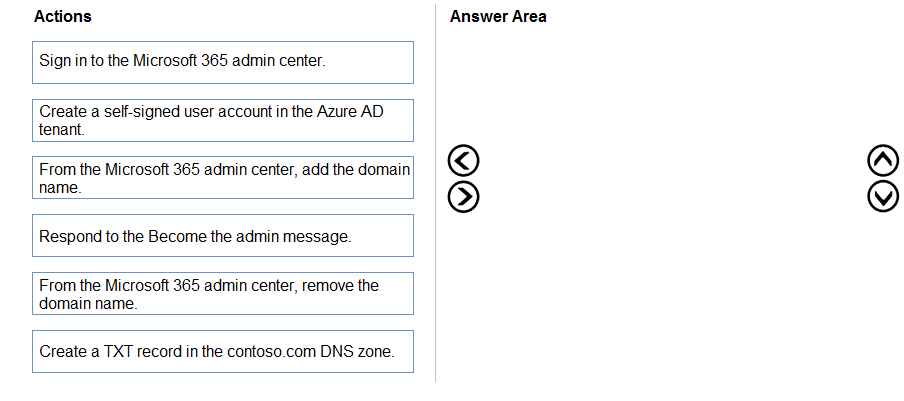
DRAG DROP - You have an on-premises Microsoft Exchange organization that uses an SMTP address space of contoso.com. You discover that users use their email address for self-service sign-up to Microsoft 365 services. You need to gain global administrator privileges to the Azure Active Directory (Azure AD) tenant that contains the self-signed users. Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order. Select and Place:
Select the correct answer(s) in the image below.
You have an Azure Active Directory (Azure AD) tenant named contoso.com. All users who run applications registered in Azure AD are subject to conditional access policies. You need to prevent the users from using legacy authentication. What should you include in the conditional access policies to filter out legacy authentication attempts?
HOTSPOT - You have an Azure Active Directory (Azure AD) tenant named contoso.com that contains a user named User1. User1 has the devices shown in the following table.
On November 5, 2020, you create and enforce terms of use in contoso.com that has the following settings: ✑ Name: Terms1 ✑ Display name: Contoso terms of use ✑ Require users to expand the terms of use: On ✑ Require users to consent on every device: On ✑ Expire consents: On ✑ Expire starting on: December 10, 2020 ✑ Frequency: Monthly On November 15, 2020, User1 accepts Terms1 on Device3. For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point. Hot Area:
Device1 with Platform Windows 10 is Registered in contoso.com.
Device2 with Platform Windows 10 is Registered in contoso.com.
Device3 with Platform iOS is Registered in contoso.com.
On November 20, 2020, User1 can accept Terms1 on Device1.
On December 11, 2020, User1 can accept Terms1 on Device2.
On December 7, 2020, User1 can accept Terms1 on Device3.
You have an Azure Active Directory (Azure AD) tenant that contains the following objects. ✑ A device named Device1 ✑ Users named User1, User2, User3, User4, and User5 Five groups named Group1, Group2, Group3, Group4, and Group5
The groups are configured as shown in the following table.
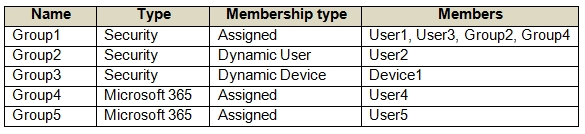
How many licenses are used if you assign the Microsoft 365 Enterprise E5 license to Group1?
Select the correct answer(s) in the image below.

HOTSPOT - You need to identify which roles to use for managing role assignments. The solution must meet the delegation requirements. What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point. Hot Area:
To manage Azure AD built-in role assignments, use: ______
To manage Azure built-in role assignments, use: ______
Ingin berlatih semua soal di mana saja?
Unduh Cloud Pass — termasuk tes latihan, pelacakan progres & lainnya.
You have an Azure Active Directory (Azure AD) tenant named contoso.com that has Azure AD Identity Protection enabled. You need to implement a sign-in risk remediation policy without blocking user access. What should you do first?
You have an Azure subscription that contains the resources shown in the following table.
For which resources can you create an access review?
Group1 is a Group that has the Assigned membership type.
App1 is an Enterprise application in Azure Active Directory (Azure AD).
Contributor is an Azure subscription role.
Role1 is an Azure Active Directory (Azure AD) role.
HOTSPOT - Your network contains an on-premises Active Directory domain named contoso.com. The domain contains the objects shown in the following table.
You install Azure AD Connect. You configure the Domain and OU filtering settings as shown in the Domain and OU Filtering exhibit. (Click the Domain and OU Filtering tab.)
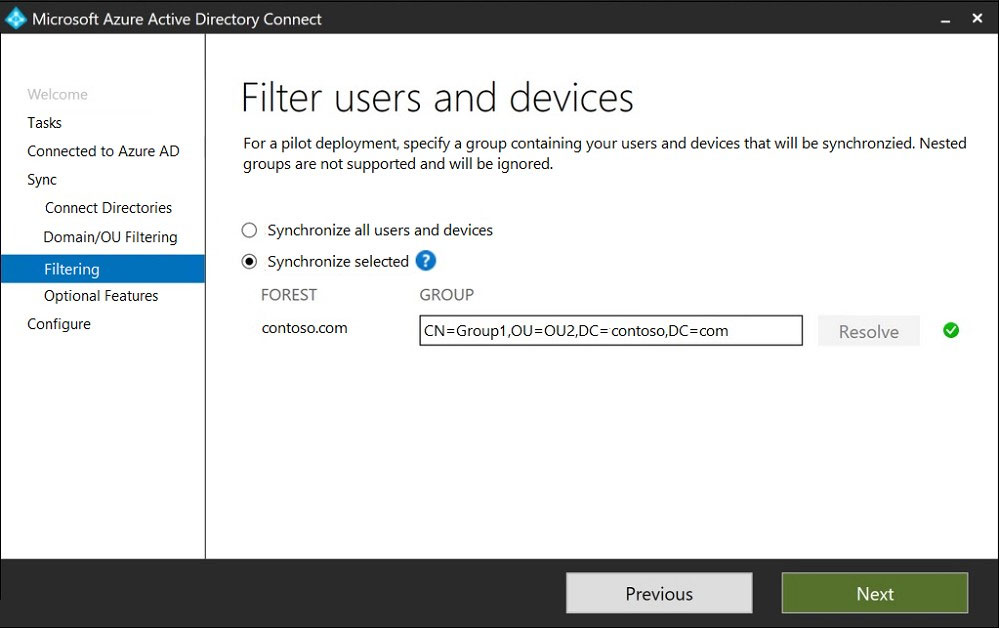
You configure the Filter users and devices settings as shown in the Filter Users and Devices exhibit. (Click the Filter Users and Devices tab.)
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point. Hot Area:
User1 is a member of Group1.
User2 is not a member of any groups.
User1 and Group2 are members of Group1.
Group2 is a member of Group1.
Select the correct answer(s) in the image below.
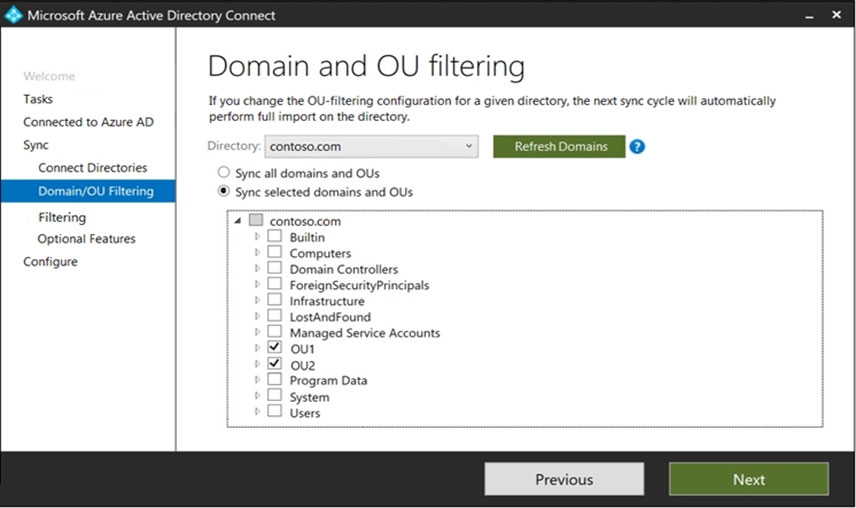
User1 syncs to Azure AD.
User2 syncs to Azure AD.
Group2 syncs to Azure AD.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution. After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen. You have a Microsoft 365 tenant. All users must use the Microsoft Authenticator app for multi-factor authentication (MFA) when accessing Microsoft 365 services. Some users report that they received an MFA prompt on their Microsoft Authenticator app without initiating a sign-in request. You need to block the users automatically when they report an MFA request that they did not initiate. Solution: From the Azure portal, you configure the Block/unblock users settings for multi-factor authentication (MFA). Does this meet the goal?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution. After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen. You use Azure Monitor to analyze Azure Active Directory (Azure AD) activity logs. You receive more than 100 email alerts each day for failed Azure AD user sign-in attempts. You need to ensure that a new security administrator receives the alerts instead of you. Solution: From Azure AD, you create an assignment for the Insights administrator role. Does this meet the goal?
Dapatkan aplikasi
