
Practice Test #1
Simulate the real exam experience with 50 questions and a 100-minute time limit. Practice with AI-verified answers and detailed explanations.
AI-Powered
Triple AI-Verified Answers & Explanations
Every answer is cross-verified by 3 leading AI models to ensure maximum accuracy. Get detailed per-option explanations and in-depth question analysis.
Practice Questions
Your company uses Azure Sentinel to manage alerts from more than 10,000 IoT devices. A security manager at the company reports that tracking security threats is increasingly difficult due to the large number of incidents. You need to recommend a solution to provide a custom visualization to simplify the investigation of threats and to infer threats by using machine learning. What should you include in the recommendation?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution. After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen. You use Azure Security Center. You receive a security alert in Security Center. You need to view recommendations to resolve the alert in Security Center. Solution: From Regulatory compliance, you download the report. Does this meet the goal?
You are configuring Azure Sentinel. You need to send a Microsoft Teams message to a channel whenever a sign-in from a suspicious IP address is detected. Which two actions should you perform in Azure Sentinel? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution. After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen. You use Azure Security Center. You receive a security alert in Security Center. You need to view recommendations to resolve the alert in Security Center. Solution: From Security alerts, you select the alert, select Take Action, and then expand the Prevent future attacks section. Does this meet the goal?
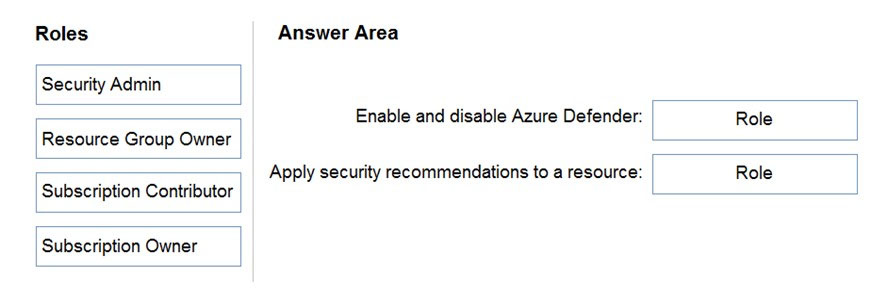
DRAG DROP - You have an Azure subscription. You need to delegate permissions to meet the following requirements: ✑ Enable and disable Azure Defender. ✑ Apply security recommendations to resource. The solution must use the principle of least privilege. Which Azure Security Center role should you use for each requirement? To answer, drag the appropriate roles to the correct requirements. Each role may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. NOTE: Each correct selection is worth one point. Select and Place:
Select the correct answer(s) in the image below.
Want to practice all questions on the go?
Download Cloud Pass — includes practice tests, progress tracking & more.
HOTSPOT - You deploy Azure Sentinel. You need to implement connectors in Azure Sentinel to monitor Microsoft Teams and Linux virtual machines in Azure. The solution must minimize administrative effort. Which data connector type should you use for each workload? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point. Hot Area:
Microsoft Teams: ______
Linux virtual machines in Azure: ______
You are configuring Azure Sentinel. You need to send a Microsoft Teams message to a channel whenever an incident representing a sign-in risk event is activated in Azure Sentinel. Which two actions should you perform in Azure Sentinel? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
You create a hunting query in Azure Sentinel. You need to receive a notification in the Azure portal as soon as the hunting query detects a match on the query. The solution must minimize effort. What should you use?
HOTSPOT - You need to recommend remediation actions for the Azure Defender alerts for Fabrikam. What should you recommend for each threat? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point. Hot Area:
Internal threat: ______
External threat: ______
HOTSPOT - You have an Azure subscription that uses Azure Defender. You plan to use Azure Security Center workflow automation to respond to Azure Defender threat alerts. You need to create an Azure policy that will perform threat remediation automatically. What should you include in the solution? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point. Hot Area:
Set available effects to: ______
To perform remediation use: ______
Other Practice Tests
Get the app
