
Practice Test #1
Simulate the real exam experience with 50 questions and a 100-minute time limit. Practice with AI-verified answers and detailed explanations.
AI-Powered
Triple AI-Verified Answers & Explanations
Every answer is cross-verified by 3 leading AI models to ensure maximum accuracy. Get detailed per-option explanations and in-depth question analysis.
Practice Questions
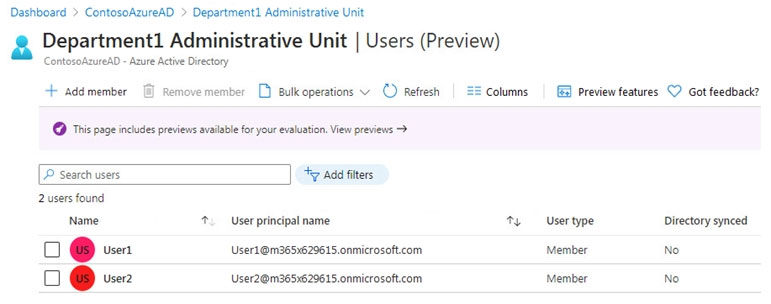
HOTSPOT - You have an Azure Active Directory (Azure AD) tenant that contains a group named Group3 and an administrative unit named Department1. Department1 has the users shown in the Users exhibit. (Click the Users tab.)
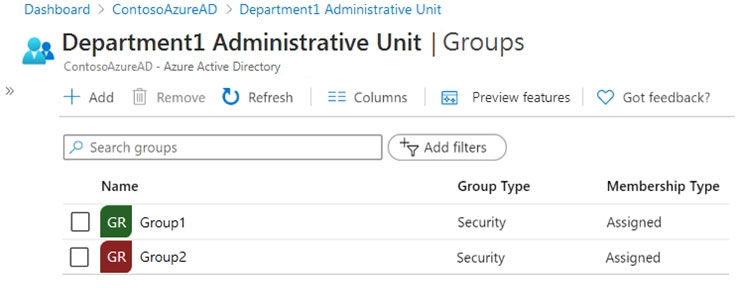
Department1 has the groups shown in the Groups exhibit. (Click the Groups tab.)
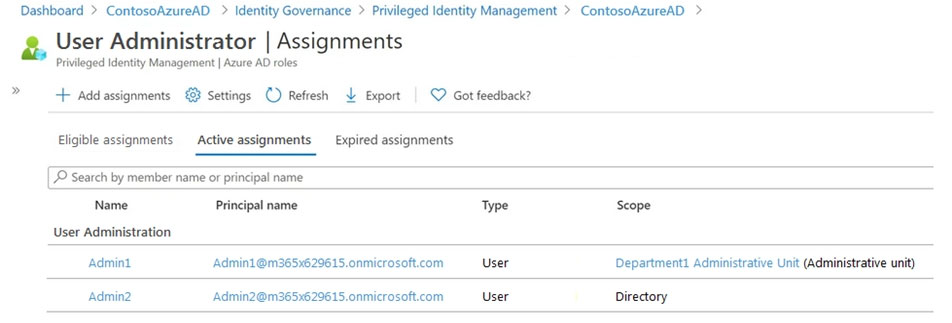
Department1 has the user administrator assignments shown in the Assignments exhibit. (Click the Assignments tab.)
The members of Group2 are shown in the Group2 exhibit. (Click the Group2 tab.)
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point. Hot Area:
Select the correct answer(s) in the image below.
Select the correct answer(s) in the image below.
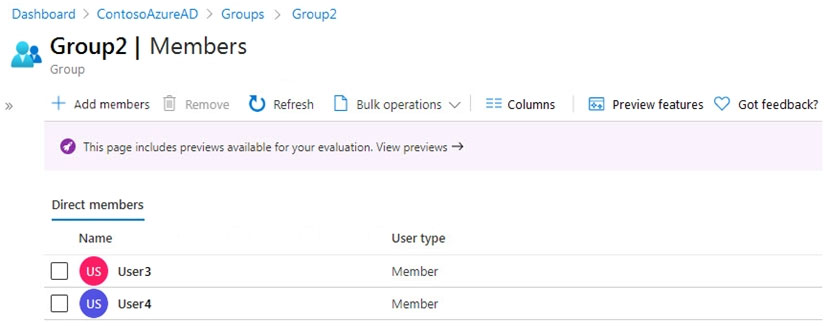
Admin1 can reset the passwords of User3 and User4.
Admin1 can add User1 to Group 2.
Admin 2 can reset the password of User1.
You have a Microsoft 365 tenant. The Sign-ins activity report shows that an external contractor signed in to the Exchange admin center. You need to review access to the Exchange admin center at the end of each month and block sign-ins if required. What should you create?
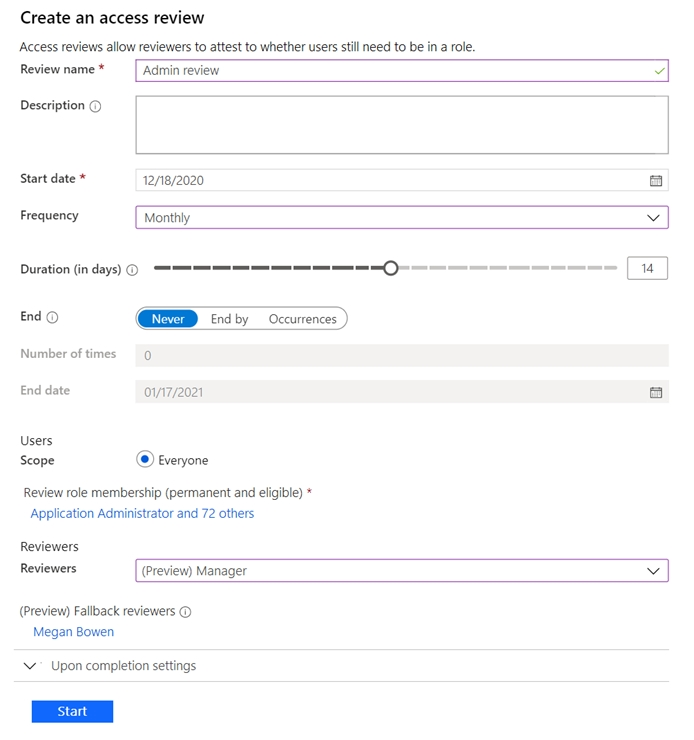
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution. After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen. You have a Microsoft 365 tenant. You have 100 IT administrators who are organized into 10 departments. You create the access review shown in the exhibit. (Click the Exhibit tab.)
You discover that all access review requests are received by Megan Bowen. You need to ensure that the manager of each department receives the access reviews of their respective department. Solution: You modify the properties of the IT administrator user accounts. Does this meet the goal?
Select the correct answer(s) in the image below.
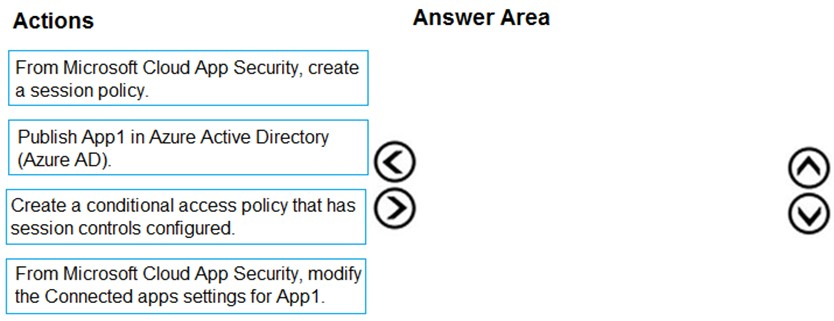
DRAG DROP - You have a Microsoft 365 E5 tenant. You purchase a cloud app named App1. You need to enable real-time session-level monitoring of App1 by using Microsoft Cloud App Security. In which order should you perform the actions? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order. Select and Place:
Select the correct answer(s) in the image below.
Your network contains an Active Directory forest named contoso.com that is linked to an Azure Active Directory (Azure AD) tenant named contoso.com by using Azure AD Connect. You need to prevent the synchronization of users who have the extensionAttribute15 attribute set to NoSync. What should you do in Azure AD Connect?
Want to practice all questions on the go?
Download Cloud Pass — includes practice tests, progress tracking & more.
You need to track application access assignments by using Identity Governance. The solution must meet the delegation requirements. What should you do first?
DRAG DROP - You have a Microsoft 365 E5 subscription that contains three users named User1, User2, and User3. You need to configure the users as shown in the following table.
Which portal should you use to configure each user? To answer, drag the appropriate portals to the correct users. Each portal may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. NOTE: Each correct selection is worth one point. Select and Place:
User1: User administrator role
User1: Device Administrators role
User1: Identity Governance Administrator role
User2: Records Management role
User2: Quarantine Administrator role group
User3: Endpoint Security Manager role
User3: Intune Role Administrator role
User1: ______
User2: ______
User3: ______
You have an Azure Active Directory (Azure AD) tenant named contoso.com. You implement entitlement management to provide resource access to users at a company named Fabrikam, Inc. Fabrikam uses a domain named fabrikam.com. Fabrikam users must be removed automatically from the tenant when access is no longer required. You need to configure the following settings: ✑ Block external user from signing in to this directory: No ✑ Remove external user: Yes ✑ Number of days before removing external user from this directory: 90 What should you configure on the Identity Governance blade?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution. After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen. You use Azure Monitor to analyze Azure Active Directory (Azure AD) activity logs. You receive more than 100 email alerts each day for failed Azure AD user sign-in attempts. You need to ensure that a new security administrator receives the alerts instead of you. Solution: From Azure AD, you modify the Diagnostics settings. Does this meet the goal?
You have an Azure Active Directory (Azure AD) tenant that: contains a user named User1. You need to ensure that User1 can create new catalogs and add1 resources to the catalogs they own. What should you do?
Get the app
