
Practice Test #5
Simulate the real exam experience with 50 questions and a 100-minute time limit. Practice with AI-verified answers and detailed explanations.
AI-Powered
Triple AI-Verified Answers & Explanations
Every answer is cross-verified by 3 leading AI models to ensure maximum accuracy. Get detailed per-option explanations and in-depth question analysis.
Practice Questions
You have an app named App1 that runs on two Azure virtual machines named VM1 and VM2. You plan to implement an Azure Availability Set for App1. The solution must ensure that App1 is available during planned maintenance of the hardware hosting VM1 and VM2. What should you include in the Availability Set?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution. After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen. You need to ensure that an Azure Active Directory (Azure AD) user named Admin1 is assigned the required role to enable Traffic Analytics for an Azure subscription. Solution: You assign the Owner role at the subscription level to Admin1. Does this meet the goal?
You have an Azure virtual machine named VM1 that runs Windows Server 2019. You save VM1 as a template named Template1 to the Azure Resource Manager library. You plan to deploy a virtual machine named VM2 from Template1. What can you configure during the deployment of VM2?
HOTSPOT - You have several Azure virtual machines on a virtual network named VNet1. You configure an Azure Storage account as shown in the following exhibit.
Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic. NOTE: Each correct selection is worth one point. Hot Area:
Select the correct answer(s) in the image below.
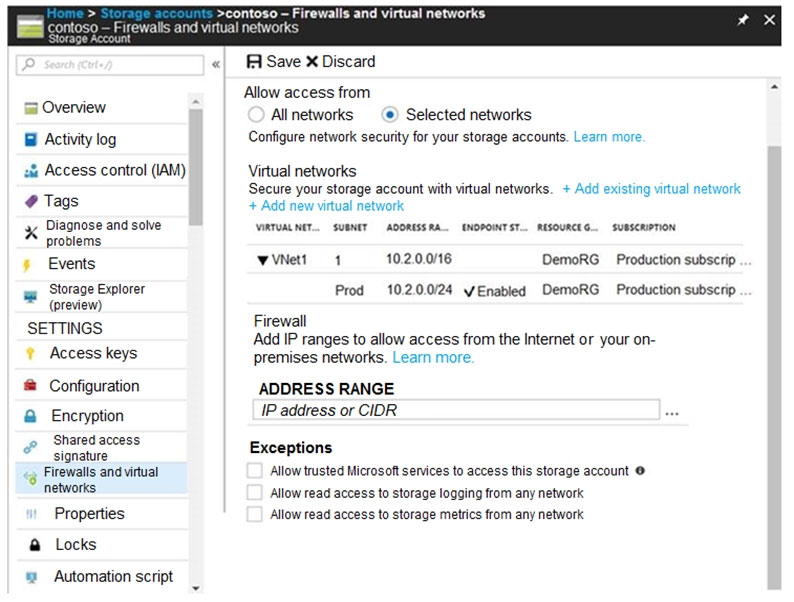
The virtual machines on the 10.2.9.0/24 subnet will have network connectivity to the file shares in the storage account ______.
Azure Backup will be able to back up the unmanaged hard disks of the virtual machines in the storage account ______.
You have an Azure Active Directory (Azure AD) tenant named adatum.com that contains the users shown in the following table.
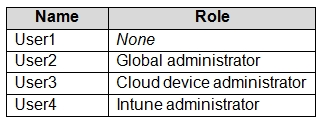
Adatum.com has the following configurations: ✑ Users may join devices to Azure AD is set to User1. ✑ Additional local administrators on Azure AD joined devices is set to None. You deploy Windows 10 to a computer named Computer1. User1 joins Computer1 to adatum.com. You need to identify the local Administrator group membership on Computer1. Which users are members of the local Administrators group?
Want to practice all questions on the go?
Download Cloud Pass — includes practice tests, progress tracking & more.
You have an Azure Active Directory (Azure AD) tenant named contoso.onmicrosoft.com.
The User administrator role is assigned to a user named Admin1.
An external partner has a Microsoft account that uses the [email protected] sign in.
Admin1 attempts to invite the external partner to sign in to the Azure AD tenant and receives the following error message: Unable to invite user [email protected] " Generic authorization exception.`
You need to ensure that Admin1 can invite the external partner to sign in to the Azure AD tenant.
What should you do?
HOTSPOT - You have an Azure subscription named Subscription1 that contains the quotas shown in the following table. Quota Location Usage Standard BS Family vCPUs West US 0 of 20 Standard D Family vCPUs West US 0 of 20 Total Regional vCPUs West US 0 of 20 You deploy virtual machines to Subscription1 as shown in the following table.
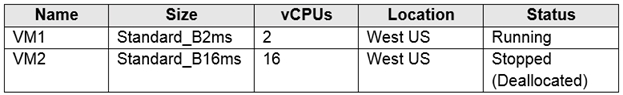
You plan to deploy the virtual machines shown in the following table. Name Size vCPUs VM3 Standard_B2ms 1 VM4 Standard_D4s_v3 4 VM5 Standard_B16ms 16 For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point. Hot Area:
You can deploy VM3 to West US.
You can deploy VM4 to West US.
You can deploy VM5 to West US.
You have an Azure subscription named Subscription1. Subscription1 contains a virtual machine named VM1. You have a computer named Computer1 that runs Windows 10. Computer1 is connected to the Internet. You add a network interface named vm1173 to VM1 as shown in the exhibit. (Click the Exhibit tab.)
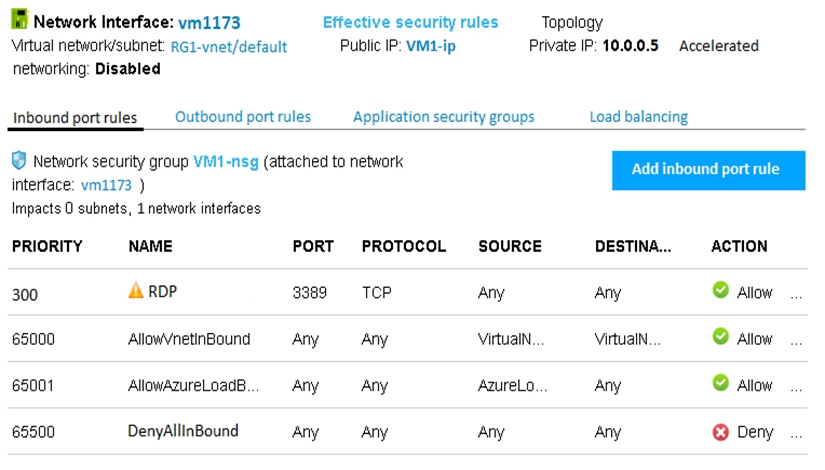
From Computer1, you attempt to connect to VM1 by using Remote Desktop, but the connection fails. You need to establish a Remote Desktop connection to VM1. What should you do first?
You have an Azure subscription named Subscription1 that contains an Azure virtual machine named VM1. VM1 is in a resource group named RG1. VM1 runs services that will be used to deploy resources to RG1. You need to ensure that a service running on VM1 can manage the resources in RG1 by using the identity of VM1. What should you do first?
You need to meet the user requirement for Admin1. What should you do?
Other Practice Tests
Practice Test #1
Practice Test #2
Practice Test #3
Practice Test #4
Practice Test #6
Practice Test #7
Practice Test #8
Practice Test #9
Get the app
